Étudier dans notre Université
Trouvez votre programme d’études
- Programmes de bachelor et de master Découvrez notre gamme de formations
- Écoles doctorales En savoir plus sur nos écoles doctorales
- Diplômes d’études spécialisées Nos offres de formation pour les futurs médecins spécialistes
- Formation continue Découvrez les possibilités de formation professionnelle et d’apprentissage tout au long de la vie
Actualités
-

Explorer l’avenir des technologies quantiques
Relations avec le publicInformatique & TICLearn more -

-

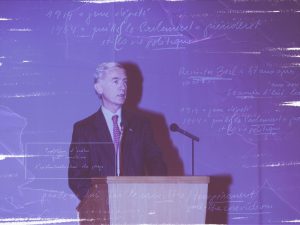
Ban Ki-moon aux étudiants d’Uni.lu : “décideurs de demain, soyez des citoyens du monde”
Relations avec le publicSciences humainesLearn more -
Un héritage d’étude et de recherche historique
Relations avec le publicSciences humainesLearn more -

Détecter les troubles de l’apprentissage : les tests adaptés aux réalités du Luxembourg
EducationÉducation & intervention socialeLearn more -

Maladie de Parkinson, un partenariat public-privé pour évaluer le potentiel d’une nouvelle molécule
RechercheSciences de la vie & médecineLearn more




